Standard installation#
This topic provides guidance on installing Anaconda Server and verifying your installation.
Note
To successfully install Anaconda Server, you must have already prepared your environment according to the Standard environment preparation topic.
Installing Anaconda Server#
Download your installer by running the following command:
# Replace <INSTALLER_LOCATION> with the provided installer URL curl -O <INSTALLER_LOCATION>
Caution
If you do not have root access, you must add yourself to the docker group by running the following command before you install:
# Replace <USERNAME> with your Anaconda username usermod -a -G docker <USERNAME>
Run one of the following installation commands. Choose the command that corresponds with your setup.
# Replace <INSTALLER> with the installer you just downloaded # Replace <FQDN> with the fully qualified domain name of your Anaconda Server instance sudo bash <INSTALLER> --keep -- --domain <FQDN> --default-user anaconda 2>&1 | tee as.install.output
If you are using TLS/SSL certificates, run this command to install Anaconda Server:
# Replace <INSTALLER> with the installer you just downloaded # Replace <FQDN> with the fully qualified domain name of your Anaconda Server instance # Replace <PATH_TO_CERT> with the path to your TLS/SSL cert # Replace <PATH_TO_KEY> with the path to your TLS/SSL key sudo bash <INSTALLER> --keep -- --domain <FQDN> --tls-cert <PATH_TO_CERT> --tls-key <PATH_TO_KEY> --default-user anaconda 2>&1 | tee as.install.output
To include Grafana monitoring dashboards in your installation of Anaconda Server, add the following argument to your installation command:
--grafana-monitor-stack
For example:
sudo bash <INSTALLER> --keep -- --domain <FQDN> --grafana-monitor-stack --default-user anaconda 2>&1 | tee as.install.output
Caution
You must be using Postgres version 9.6 or later and Redis version 6.0 or later.
# Replace <INSTALLER> with the installer file you just downloaded # Replace <FQDN> with the fully qualified domain name of your Anaconda Server instance # Replace <PATH_TO_CERT> with the path to your TLS/SSL cert # Replace <PATH_TO_KEY> with the path to your TLS/SSL key # Replace <EXTERNAL_PS/RD_INSTANCE_IP4> with your external instance IP4 address (in both locations) # Replace <ASSIGNED_PORT> with the port used for communication # Replace <POSTGRES_USERID> with your postgres user ID # Replace <POSTGRES_PASSWORD> with your postgres password chmod +x <INSTALLER> bash <INSTALLER> --keep -- --domain <FQDN> --tls-cert <PATH_TO_CERT> --tls-key <PATH_TO_KEY> -e redis://<EXTERNAL_PS/RD_INSTANCE_IP4> -h <EXTERNAL_PS/RD_INSTANCE_IP4> -p <ASSIGNED_PORT> -u <POSTGRES_USERID> -pw <POSTGRES_PASSWORD> --default-user anaconda -y 2>&1 | tee as.install.output
The installation process creates two distinct user profiles: one for administrating Anaconda Server and one for administrating Keycloak. Login credentials for these profiles are shown during the installer output. Use these credentials for your initial login, and update them as soon as possible.
Example output
KeyCloak admin user: 'admin' KeyCloak admin password: 'B1EpU33Wasdfh0Z64LL767cD' Updating Keycloak settings ... Default user: 'anaconda' password: '8aZ6302Ssd34ge415Ld97I'
Note
The installer directory contains both the installation script (install.sh) and the docker-compose.yml file, which defines how the Anaconda Server services are run.
By default, /opt/anaconda/repo is the file path for the installation folder. You can either create the folder manually by assigning write access to the current user, or use the -b (--base-install-dir) parameter to specify the folder for your installation.
Warning
Never delete the directory containing the docker-compose.yml and .env files.
Verifying your installation#
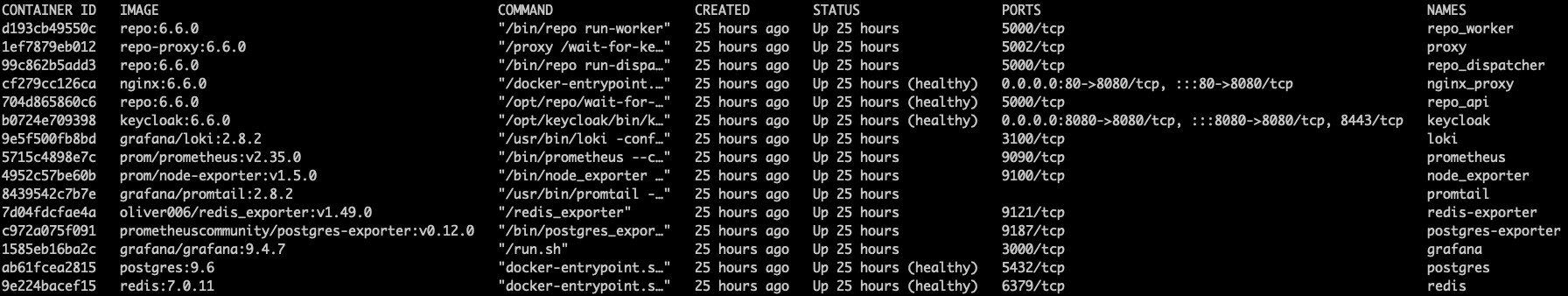
Services are one-to-one to containers. Therefore, verifying that all major containers are up and not restarting or failing is a good first step.
Return to your terminal and run the following command:
Verify that the following containers appear with a
STATUSofUp(not stuck in a restart loop) in the output:repo_api repo_worker repo_dispatcher proxy nginx_proxy keycloak redis postgres
These containers should always be running. However, you might see additional containers, depending on the phase of installation or your initial configuration choices:
Additional containers
loki grafana promtail prometheus node_exporter redis-exporter postgres-exporter
Open a browser and navigate to the domain that you supplied when executing the installer. If you are able to successfully authenticate and are asked for a license, Package Security Manager has installed successfully.
Advanced options#
Further installation options can be seen by running the following command:
# Replace <INSTALLER> with your installer file
./<INSTALLER>/install.sh --help
This will present you with the following list of possible arguments:
Arguments (shorthand) |
Arguments (longhand) |
Description |
|
|
Docker registry, url:port (default uses the system Docker daemon) |
|
|
Postgresql host (default is on internal Postgres instance) |
|
|
Postgresql port |
|
|
Postgresql user |
|
|
Postgresql password (will set the internal Postgres instance password) |
|
|
Redis URL (default is an internal Redis instance) |
|
|
External domain (or IP) of host system |
|
|
Path to TLS certification file for optionally configuring HTTPS |
|
|
Path to TLS key file for optionally configuring HTTPS |
|
Default user name |
|
|
Path to custom CA certification, which should be respected |
|
|
For Airgaped environments provide a custom source for CVE data |
|
|
Previous install folder |
|
|
|
Don’t load Docker images |
|
|
Answer yes to all prompts |
|
Print help text |